Number of hours
- Lectures 12.0
- Projects -
- Tutorials 6.0
- Internship -
- Laboratory works 9.0
- Written tests -
ECTS
ECTS 3.0
Goal(s)
After the course, the student should be able to:
- analyze the security needs of a communication and/or computation system at an algorithmic/informational level;
- find trivial flaws in (in)secure protocol proposals;
- grasp the design principles and security stakes of cryptographic primitives;
- implement a cryptographic primitive (hardware or embedded) knowing its specification.
Responsible(s)
Yann KIEFFER
Content(s)
- The need for cryptographic primitives and protocols;
- Symmetric cryptosystems: design, make-up, analysis;
- Security features of protocols;
- Security assessment of cryptographic protocols;
- Arithmetic for asymmetric cryptography;
- Examples of asymmetric cryptosystems;
- Implementations of cryptographic primitives.
Hardware design courses: digital design, VHDL, FPGA.
Embedded application design.
Test
E1: result of end-term written exam (90 min)
E2: individual oral examination (30 min)
CC: semester-long assessment
Documents and calculators authorized for all exams
Additional Information
Course ID : 5AMSE516
Course language(s):
You can find this course among all other courses.
Bibliography
The code book: the science of secrecy from ancient Egypt to quantum cryptography, Simon Singh; Anchor.
Cryptography - a very short introduction, Fred Piper & Sean Murphy; Oxford university press.
Understanding cryptography - a textbook for students and practitioners, Christoph Paar, Jan Pelzl; Springer.
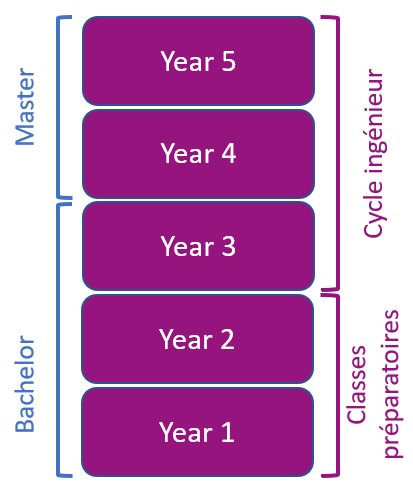
What is a grande école ?
French engineering curriculum