Informations générales
Number of hours
- Lectures 15.0
- Projects -
- Tutorials -
- Internship -
- Laboratory works 12.0
- Written tests -
ECTSECTS
2.5
Goal(s)
After the course, the student should be able to:
- analyze the security needs of a communication and/or computation system;
- use general knowledge about cryptographic primitives;
- analyse the fitness of a secure solution with regards to cost and use constraints.
Responsible(s)
Oum-El-Kheir AKTOUF
Content(s)
- Models for security analysis.
- Shannon's theory, perfect security, Kerckhoff's principle.
- Symmetric cryptosystems: design, make-up, analysis.
- Other protocols and algorithms.
- Asymetric cryptosystems.
- Applications.
Conditional probability.
Knowledge of Z/nZ (inverse elements, powers, primitive roots).
Test
E1: written exam, session 1: 1h30 min. Documents and calculators can be used.
E2: oral exam, session 2: 30 min. Documents and calculators can be used.
TP: lab sessions evaluation.
P: presentation.
The exam is given in english only 
Calendar
The course exists in the following branches:
- Curriculum - Network and computer science - Semester 9
Additional Information
Course ID : 5AMSE500
Course language(s): 
The course is attached to the following structures:
- Team Computer Science
You can find this course among all other courses.
Bibliography
- Cryptography, a very short introduction – Fred Piper & Sean Murphy, Oxford.
- Understanding cryptography – Christoph Paar & Jan Pelzl, Springer.
- Codes and cryptography – Dominic Welsh, Oxford.
- Cours de cryptographie – Gilles Zémor, Cassini.
- Cryptographie : théorie et pratique – Douglas Stinson, Intl Thompson Pub.
- Cryptography engineering – Neils Ferguson, Bruce Schneier & Tadayoshi Kohno,
Wiley. - Handbook of applied cryptography – Alfred Menezes, Paul Van Orschoot, Scott
Vanstone, CRC Press. (Disponible en ligne en intégralité)
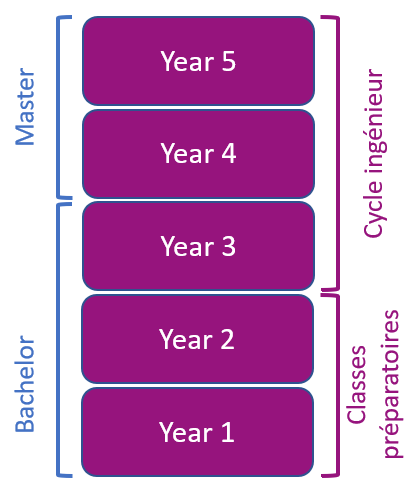
What is a grande école ?
French engineering curriculum