Advanced Processor Architecture and SoC Design - 5AMCE515 - 5 ECTS - 45h
-
The objective of this course is give to each student the minimal knowledge to design or choose a processor for a targeted application.
The students will learn the hardware architecture of a SOPC system and the associated software development to exploit the performance
of these systems.This course is mainly divided into 2 parts. In the first one, the students will design a complex system composed of a
main processor and different peripherals linked by a bus using a Xilinx Zync 7000 chip. The second part deals with the NEON engine
located inside the main processor of the Zync 7000. This engine adds a new instruction set allowing to realize multiple operations
in parallel. -
Introduction to System On Chip
- SOPC vs Embedded System
- Hardware Software Partitionning
- Processing Unit Choices (MCU vs DSP)
- System on Programmable Chip Architectures
- SOPC Design Flow
- Application Design Using SOPC
- Introduction to HLS
- Embedded Software Optimization Using Dedicated Co-Processor
Introduction to NEON
- ARM Processors
- Classification
- Instruction Sets
- ARM Assembly
- NEON Engine
- Architecture
- Assembly
- Intrinsics
- Automatic Vectorization
This course contains 2CM and 12TP and 1 Exam.
- SOPC vs Embedded System
-
- Digital design
- VHDL or Verilog
- FPGA design
- Embedded software Programming
- C
- AssemblyLanguage
- Processor Architecture
- RISC Architecture
- ARM processor
- Digital design
-
E1: Exam (1st session): Written exam 1h30, without documents, without calculator
E2: Exam (2nd session): Written exam 1h30, without documents, without calculator
TP: Labs
Verification and test of safe and secure embedded systems - 5AMSE517 - 5 ECTS - 45h
-
At the end of the lecture, the students will be able to verify and to test digital secure or critical architectures, and to analyze the robustness of embedded systemes.
General objectives:
*To be able to verify the functionalities of a design
*To be able to test its fabrication
*To be able to analyze the safety and security vulnerabilities of embedded systemsSpecific objectives:
*Functional verification techniques
*Testbenches writing, qualification, assertions, emulation, prototyping, formal approaches
for FPGA or ASIC design flows
*Hardware testing
*Fault modeling, test pattern generation, DfT, JTAG
*On-line Printed Circuit Board (PCB) testing
*Robustness and vulnerability analyses
*To be able to choose the most adapted techniques for verification and test- Advanced techniques for HardWare (HW) and SoftWare (SW) co-design and co-verification:
Virtual Prototyping
**High Level Modelling (TLM, BFM)
**Assertions (PSL)
- Advanced techniques for HardWare (HW) and SoftWare (SW) co-design and co-verification:
-
*I Introduction
**A Context and Issues
**B Verification vs Test
**C Example of Aeronautical Standard DO-254*II Hardware Verification
**A Hardware Simulation
***a languages, simulators and levels of abstraction
***b black/white box verifications
***c qualification
***d robustness measurement by fault simulation
***e writing testbench in VHDL (behavioural)
***f assertions (assert, OVL, PSL)
**B Formal verification
***a equivalence checking
***b property/model checking
**C Hardware testing
***a failures and hardware fault models
***b design for test and self test (DfT & BIST)
***c boundary scan
**C Security validation
***a fuzz testing
***b reuse of verification tools*III Hardware/Software System Co-Verification (HW/SW)
**A Introduction
**B Hardware/Software Partitioning
***a objectives
***b tools (hardware accelerators, high-level synthesis, system design flow)
**C Hardware/software co-development
***a objectives and issues
***b solutions (co-simulation, FPGA prototyping, virtual prototyping)
**D Hardware/Software Co-Verification
***a objectives and solutionsPractical work
Project 1 : VHDL simulation & PSL assertions with QuestaSim (Mentor GraphiCs)
Project 2: Hardware/software co-verification based on virtual prototyping -
Mandatory: Hardware Description Language (HDL, verilog or VHDL) for simulation (testbench) and design, logical synthesis, FPGA, processor architecture (processor models, instruction set architecture), C programming
Expected: bases of object oriented programming
-
E1 = Terminal Exam, First session, written, 2h, only document allowed "syntaxe VHDL", no calculator
TP = average of laboratory exams
E2 = Exam, Second session, written 2h, only document allowed "syntaxe VHDL", no calculator
Embedded Systems Security - 5AMSE518 - 5 ECTS - 45h
-
- Educational Objectives: This course is aimed at giving understanding about embedded system security with a focus on the hardware role on the system security. The course offers a broad spectrum of hardware vulnerabilities and associated countermeasures (designed either at the hardware or software level). The course addresses also hardware-based security schemes focusing on their system level integration. The course is based on real life examples.
- Course Outcomes: At the end of the course, the students have understanding on basic terminology and concepts related to hardware vulnerabilities embedded system security and hardware support for system security. They are also exposed to basic cryptography, certification issues and vulnerability analysis methodology. In the end, the students put it all together in the form of a case study for designing and evaluating an embedded system.
-
- Introduction to Embedded System Security
- Side Channel Attack (SCA)
- Attack Principles
- Practical Consideration and different types of SCA
- Designing practical Countermeasures against SCA
- Labs on SCA
- Fault Injection (FI) Attacks
- Objectives and Principles
- FI Means with their effect
- Case studies on HW and SW un FI
- Labs
- Trustworthy Hardware
- Trust Issues during the Integrated Circuit Life Cycle
- Test and Security
- Hardware Trojan
- Counterfeiting and Piracy
- Physical Unclonable Function (PUF)
- Principles
- Design, Integration and Evaluation of PUF
- System Level security based on PUF
- Labs
- Hardware Support for Trusted Computing
- Control Flow Integrity
- Memory Isolation
- Trusted Execution Environment
- System level integration of hardware based security
-
computer architecture, digital electronics, VHDL/Verilog, signal processing, C programming, embedded system design and test
-
continuous assessment 25% Labs 25% Final Exam 50%
Dependability and security of computing systems - 5AMSE508 - 5 ECTS - 42h
-
Students should be able to :
- determine safety properties for computing systems;
- implement appropriate fault tolerance approaches depending on the nature of studied systems;
- evaluate dependability attributes using analytical approaches;
- improve system robustness by using fault detection and elimination techniques;
- identify security requirements of a system;
- enhance the security of a system by using adequate security protection means;
- analyze safaty and security interplay.
-
Course content
I. Introduction
- Terminology and basics
II. Fault-tolerance: redundancy techniques
- Functional and structural redundancy
- Structural redundancy techniques
III. Fault prediction: dependability evaluation techniques
- Combinatorial approaches
- Markov models
- The FMEA analysis.
IV. Fault elimination: Software testing
- Goals and limitations of testing
- Testing techniques based on the program structures or on specifications
- Regression testing
- Conformance testing
V. Introduction to software security: vulnerabilities and protections
- Software vulnerabilities (Buffer overflow, Stack-based overflow, Return oriented programming...)
- Protections (Safe C library, DEP, Canary, ASLR...)
VI. Summary: safety and security
- Conflicts
- co-analysis and co-engineering
- Current standards
Tutoriel content
- Redundancy techniques
- Evaluation of dependability attributes
- Software testing
Lab works
- Reliability diagrams
- Fault trees and Markov chains
- Conformance testing
- Test tools
-
- Computer architecture
- Good programming skills
- Graph theory and probabilities basics
-
E1: session 1 final exam (written exam, 3h00, closed books, allowed calculator)
TP: 1 mark
E2: session 2 exam (written exam, 1h30, closed books, allowed calculator)
Innovation Project - 5AMPX505 - 4 ECTS - 45h
-
Assess and enhance:
- Skills for the development of multidisciplinary systems
- Work in a multidisciplinary team
- The ability to innovate
- Autonomy
-
Groups consist of at least 4 students following different specialties.
Subjects (open and multidisciplinary) are offered by responsible of 5th year module.
The job is done by each group independently; groups have access to the SACCO platform and TP classrooms of the school.
-
P1 = Mean of report evaluation and oral presentation
Cryptography and secure protocols for embedded systems - 5AMSE520 - 5 ECTS - 45h
-
After the course, the student should be able to:
- analyze the security needs of a communication and/or computation system at an algorithmic/informational level;
- find trivial flaws in (in)secure protocol proposals;
- grasp the design principles and security stakes of cryptographic primitives;
- implement a cryptographic primitive (hardware or embedded) knowing its specification.
-
- The need for cryptographic primitives and protocols;
- Symmetric cryptosystems: design, make-up, analysis;
- Security features of protocols;
- Security assessment of cryptographic protocols;
- Arithmetic for asymmetric cryptography;
- Examples of asymmetric cryptosystems;
- Implementations of cryptographic primitives.
-
Hardware design courses: digital design, VHDL, FPGA.
Embedded application design. -
E1: result of end-term written exam (90 min)
E2: individual oral examination (30 min)
CC: semester-long assessmentDocuments and calculators authorized for all exams
Decentralized control of complex systems - 5AMAC555 - 5 ECTS - 45h
-
This course reviews the past and present results in the area of decentralized control of complex dynamical systems. Elements from control theory and optimization are merged in order to provide useful tools which will be further applied to various problems involving multi-agent dynamical systems and interconnected systems in general.
An emphasis is laid on centralized vs distributed vs decentralized approaches, decomposition, information structure constraints, the stabilization and the tracking performances of each agent, robustness. The presented theory answers the fundamental questions of how to break down a given control problem into manageable subproblems which are only weakly related to each other and can be solved independently.
The tools the students will acquire during the course in optimization-based control (via distributed/hierarchical approaches) will be used for some application benchmarks like control and coordination of multiple (aerial, aquatic) drones, energy management in DC microgrid systems and water distribution networks. -
1 An optimization-based approach for control of complex systems
1.1 Introduction to the control of complex systems
1.2 Optimization-based control
1.3 Generic prediction models
1.4 Generation of a reference trajectory/profile
1.5 Set-theoretic elements
1.6 Mixed-integer representations in control design2 Challenges in decentralized control
2.1 Decentralization
2.2 Decomposition
2.3 Coupling constraints
2.4 Information exchange3 Cooperative control of multi-agent dynamical systems
3.1 System description
3.2 Collision avoidance formulation
3.3 Area coverage for multi-agent systems in multi-obstacle environment
3.4 A tight configuration of multi-agent formation
3.5 Centralized MPC
3.6 Distributed MPC
3.7 Decentralized MPC4 Stability and robustness analysis
4.1. Stability ingredients
4.2. Tube MPC introduction
5 Examples, simulations, benchmarks and applications
5.1 Flight control experiments of Unmanned Aerial Vehicles (UAVs)
5.2 Connectivity maintenance for Unmanned Surface Vehicles (USVs)
5.3 Hierarchical control for DC microgrid energy management
5.4 Decentralized supervision and control of water networks -
The course is intended for master students in applied science with a major in control. A basic knowledge in control theory (state-space representation) and Matlab/Python/C programming are required.
This module will also give some insights on the research field and will provide direction for students who want to start a PhD thesis.
-
N1= 30%xTP + 70%xFinalExam
N2= 100%FinalExam
Nconf = 100% FinalExam
FinalExam = Oral examination
French as a Foreign Language - WAMFLE - 1 ECTS - 22,5h
-
General objectives of the course:
-to consolidate language structure and both oral and written skills
-to give students the tools needed to operate in daily situations during their stay in France
Pedagogical objectives:
-help students become independent in a variety of daily situations in France -
France: understanding (listening and reading) info about France
Auvergne Rhône-Alpes Region (Lyon and Grenoble)
Drôme and Ardèche: understanding basic documents (tourism, the economy, culture)
Studying and working in France
Writing a CV and a cover letter
Making appointments over the phone
Job interviews
New Technologies
-
None
-
Methods of Evaluations : tests and quizzes
French State controlled Master's degree

What is a grande école ?
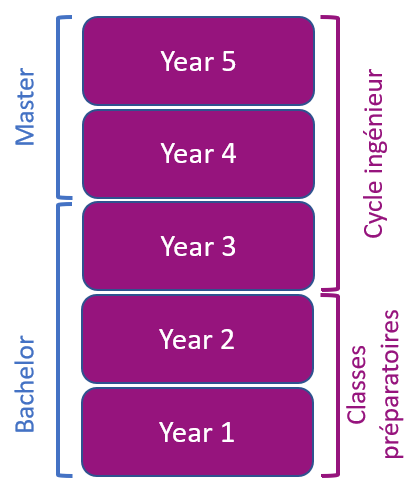
French engineering curriculum